Personal Identity Research Node Malicious Phone Number Lookup Explaining Fraud Check Queries
Malicious phone number lookup aggregates diverse signals to assess risk, balancing data minimization with practical fraud detection. Fraud check queries rely on attribution, verification gaps, and evidence-based thresholds, using behavioral, contextual, and historical indicators. Signals include anomalous call patterns, geographic mismatches, and unusual device linkage. Governance and consent processes frame transparent, auditable decisions. While privacy safeguards exist, the approach must confront trade-offs between safety and data use, leaving unresolved questions about thresholding and accountability that merit further scrutiny.
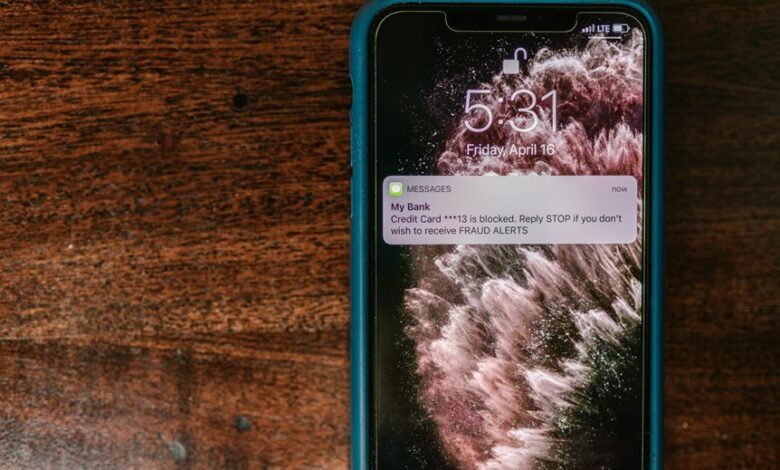
What Is Malicious Phone Number Lookup and Why It Matters
Malicious phone number lookup is the process of identifying and validating telephone numbers associated with fraudulent activity, compromised accounts, or impersonation schemes. This practice informs risk assessments and credential protection measures by revealing linkage patterns, attribution signals, and verification gaps. The discussion ideas emphasize frameworks for responsible data use, while privacy ethics constrain data access, minimize harm, and preserve individual autonomy.
How Fraud Check Queries Work Under the Hood
Fraud check queries operate by aggregating signal data from multiple sources to assess a given number’s risk profile. The process evaluates fraud signals while respecting data minimization principles, limiting collection to relevant attributes. Privacy risk is mitigated through governance and anonymization. Transparency and user consent underpin data flows, enabling auditable, evidence-based decisions without overreach.
Signals That Flag a Suspicious Phone Number
Signals that flag a suspicious phone number emerge from a structured appraisal of behavioral, contextual, and historical indicators. The assessment identifies patterns such as anomalous call frequencies, abrupt number changes, and mismatched geolocation. It classifies risks through lookup signals, enabling proactive verification without overwhelming privacy safety. Findings emphasize reproducibility, traceable data sources, and evidence-based thresholds for malicious phone detection.
Balancing Privacy, Safety, and Proactive Verification
Balancing privacy, safety, and proactive verification requires a structured assessment of trade-offs between individual rights and collective security.
The analysis emphasizes privacy risk and data minimization as core controls, ensuring proportionate data use while maintaining effective fraud checks.
Security implications duplicates are examined to prevent unnecessary duplication, reinforcing transparent governance and evidence-based safeguards that respect autonomy without compromising protective capabilities.
Conclusion
In essence, the fraud-check paradigm mirrors a careful forensic audit: disparate signals converge into a verdict with auditable provenance. The method trusts evidence over intuition, balancing risk flags with privacy safeguards. Like a lighthouse cutting through fog, attribution and verification gaps illuminate where questions remain. The resulting decisions, tethered to data minimization and consent, reinforce accountability while maintaining safety. Thus, unseen patterns become visible, guiding prudent, evidence-based judgments in a complex digital landscape.